Automate NIS2 compliance with ease
NIS2 demands cybersecurity resilience across your entire organisation. Hy5 brings the structure and automation to make it easy.

Find cybersecurity gaps before anyone else does
Security controls connected in one place
Hy5 maps security measures across departments and systems to a single compliance layer. Everything is linked and ready. No reconstruction, no guesswork.
Incident response connected to live systems
Hy5 links incident response procedures directly to the controls and systems they protect. When incidents occur, teams know exactly what to do. Reporting within 24 and 72 hours becomes a structured process, not a scramble.
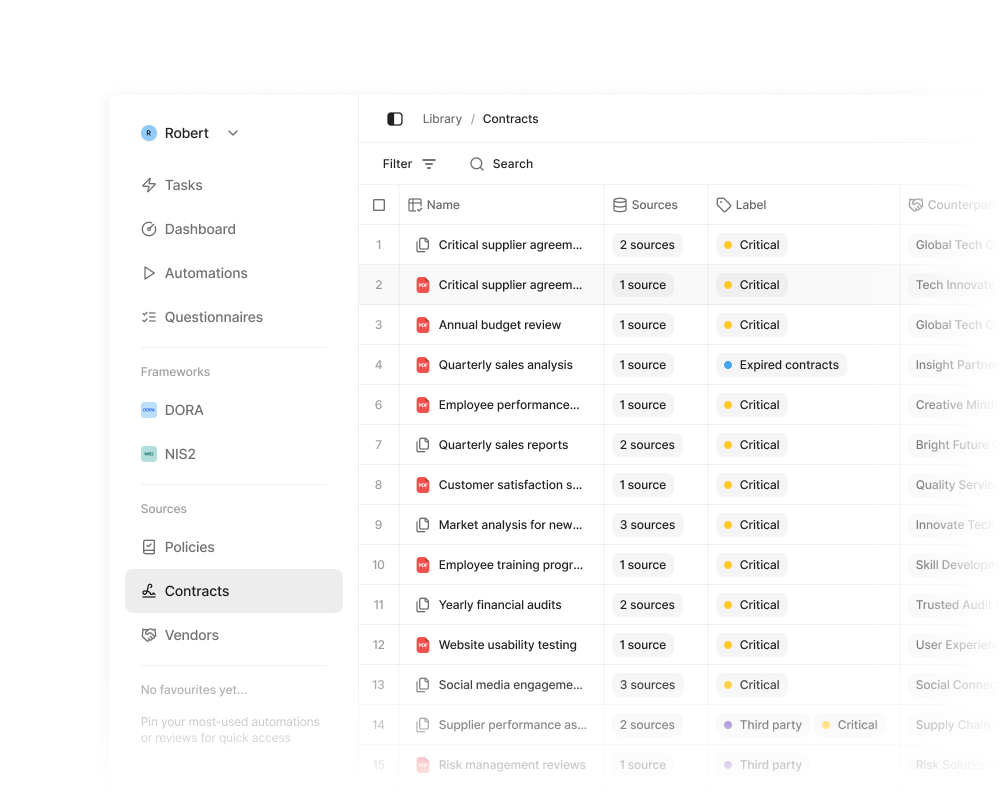
Supply chain security monitored continuously
Hy5 tracks supplier cybersecurity risks alongside your contractual obligations and assessments. Changes in supplier status surface immediately, not after they've impacted operations.
Board-level accountability made visible
Hy5 gives management a unified view of cybersecurity posture and compliance status. No aggregating fragmented reports or manual analysis. Boards can demonstrate oversight and make strategic security decisions with confidence.
“Today, we save 50% of
legal costs when applying
Hy5 in compliance reviews”
Automated compliance
for the entire organisation
One system that connects your whole organisation to your compliance requirements. Every policy, contract, and control has a clear owner. The platform supports operations with suggestions and automation, but you stay in control. Your audit trail is built by your decisions.
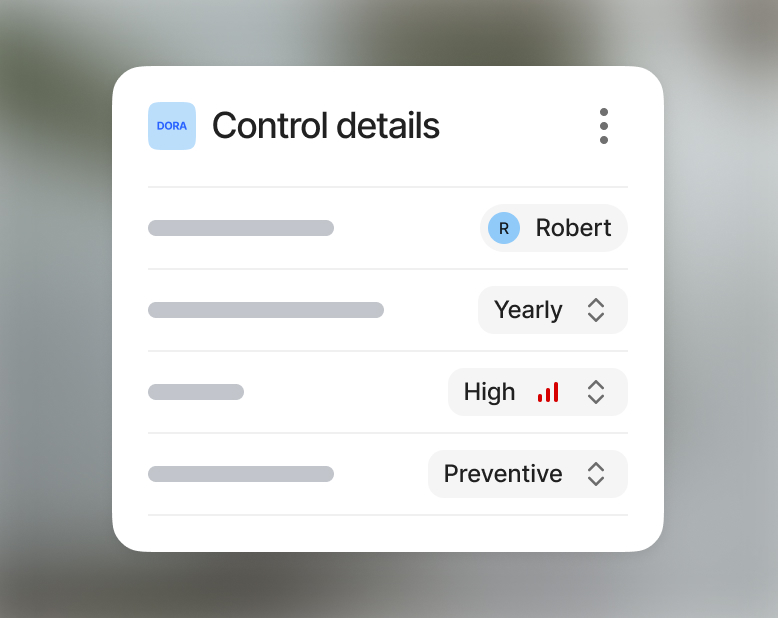
Structured requirements for compliance leaders
The foundation layer translates regulations, internal rules, and best practices into clear, configurable processes. Requirements, roles, controls, and documentation are defined and traceable.
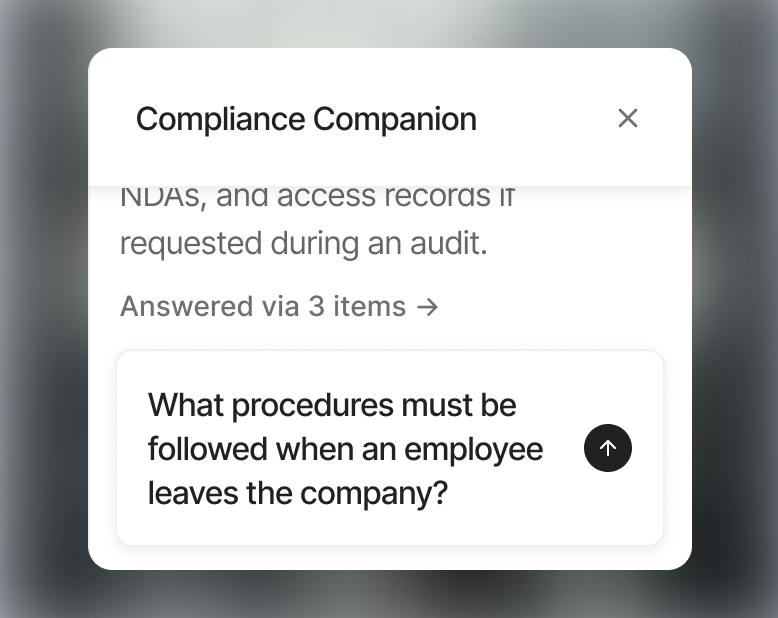
Guided execution for every employee
The operational layer takes structure to the frontline. Hy5 guides employees through tasks, automates repetitive controls, and provides AI-supported assistance for decisions. Everyone knows what to do, how to do it, and whether it's done correctly.
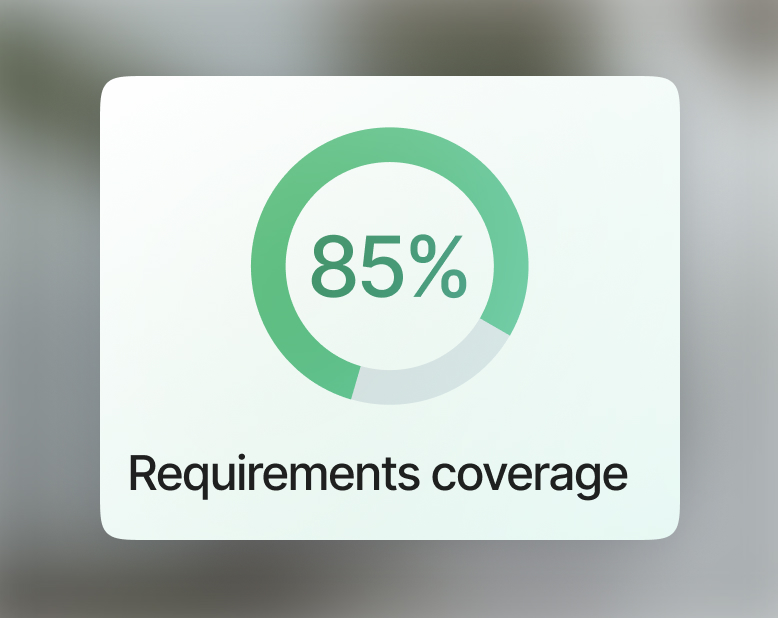
Instant reporting for leadership and stakeholders
The reporting layer gives leadership and stakeholders a clear view of the situation. Dashboards and reports make internal follow-up easy, and the same data can be shared with customers, suppliers, and authorities when needed.
NIS2 mandates cybersecurity across critical infrastructure
The revised Network and Information Systems Directive is an EU regulation that came into force on 17 October 2024. It establishes stricter cybersecurity requirements for critical and essential entities across eighteen sectors.
NIS2 applies to medium and large organisations across eighteen sectors, divided into two categories:
Essential entities (highly critical sectors): Energy, transport, banking, financial market infrastructure, healthcare, drinking water, wastewater, digital infrastructure, ICT service management (B2B), public administration, and space.
Important entities (other critical sectors): Postal and courier services, waste management, chemicals, food production and distribution, manufacturing (including medical devices, automotive, and transport equipment), digital providers (marketplaces, search engines, social networks), and research.
The general threshold is 50 or more employees, or annual turnover exceeding €10 million. Smaller organisations may still be in scope if they provide critical services.
NIS2 requires all entities in scope to implement ten minimum cybersecurity risk-management measures:
- Risk analysis and information system security policies
- Incident handling — detection, response, and reporting within 24 and 72 hours
- Business continuity and crisis management — including backup and disaster recovery
- Supply chain security — assessing the cybersecurity posture of direct suppliers and service providers
- Security in network and information systems — acquisition, development, and maintenance, including vulnerability handling
- Policies and procedures to assess cybersecurity effectiveness — regular testing and auditing
- Basic cyber hygiene practices and cybersecurity training — at all organisational levels
- Policies on the use of cryptography and encryption
- Human resources security, access control policies, and asset management
- Multi-factor authentication and secured communication systems
Organisations must also report significant incidents to their national CSIRT: an early warning within 24 hours, a detailed notification within 72 hours, and a final report within one month.
You must implement the ten minimum security measures, register with your national supervisory authority, and report significant incidents within strict timeframes. Leadership is held personally accountable for compliance.
Non-compliance carries serious consequences:
- Essential entities: fines up to €10 million or 2% of global annual turnover, whichever is higher
- Important entities: fines up to €7 million or 1.4% of global annual turnover, whichever is higher
- Management liability: individuals in leadership roles can face temporary bans or disqualification
- Operational restrictions: authorities may suspend certifications, authorisations, or operations
NIS2 shifts cybersecurity from a technical concern to a board-level legal obligation.
NIS2 significantly expands the scope and enforcement of the original 2016 directive:
- Broader scope: from 7 sectors to 18, covering an estimated 160,000+ entities across the EU
- Size-based thresholds: medium organisations (50+ employees or €10M+ turnover) are now in scope
- Stricter incident reporting: mandatory 24-hour early warning, 72-hour notification, and one-month final report
- Personal accountability: management bodies are directly liable for compliance failures
- Harmonised enforcement: minimum fine thresholds set at EU level, reducing inconsistency between member states
- Supply chain focus: organisations must assess the cybersecurity posture of their direct suppliers
NIS2 establishes obligations across four areas:
- Cybersecurity risk management — implement the ten minimum security measures proportionate to your risk exposure
- Incident reporting — notify national authorities of significant incidents within 24 hours (early warning), 72 hours (detailed notification), and one month (final report)
- Governance and accountability — management bodies must approve cybersecurity measures, oversee their implementation, and undergo training. They can be held personally liable for failures.
- Supervision and enforcement — national authorities conduct audits, inspections, and can issue binding instructions. Essential entities face proactive supervision; important entities face reactive supervision after an incident.
The directive applies proportionately. Essential entities face stricter oversight than important entities, but neither category is exempt from the core obligations.
Sweden transposed NIS2 into national law through the Cybersecurity Act (Cybersäkerhetslagen, 2025:1506) and the Cybersecurity Ordinance (2025:1507), both in force since 15 January 2026.
Key aspects of the Swedish implementation:
- Whole-entity approach: obligations extend across entire organisations, not just IT departments
- Decentralised supervision: the Swedish Civil Contingencies Agency (MSB) oversees most sectors, while the Swedish Energy Agency supervises the energy sector
- Nine security areas: incident handling, business continuity, supply chain security, secure development, cryptography, personnel security, access control, secure communication, and authentication
- Registration required: covered entities must register with their supervisory authority
- Management training: the Act places explicit demands on management participation in cybersecurity work
Contact sales
Leave your details and we'll get back to you shortly.